A cloud service provider just launched a new serverless service that is compliant with all security regulations. A company deployed its code using the service, and the company's application was hacked due to leaked credentials. Which of the following is responsible?
A software engineer at a cybersecurity company wants to access the cloud environment. Per company policy, the cloud environment should not be directly accessible via the internet. Which of the following options best describes how the software engineer can access the cloud resources?
A cloud engineer must find the root cause of a recent performance issue. Logs and metrics have been collected and are available. Which of the following is the best way to determine the source of the issue?
A developer is building a new application version using a CI/CD pipeline. The developer receives the following error message log when the build fails:
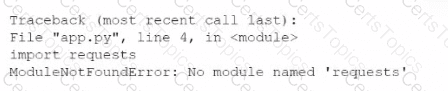
Which of the following is the most likely cause of this failure?