Which two package management tools can be used to configure and install applications on VMware vSphere Kubernetes Service (VKS)? (Choose two.)
What open-source project enables automated lifecycle management of VMware vSphere Kubernetes Service (VKS) clusters?
What statement describes Cluster API?
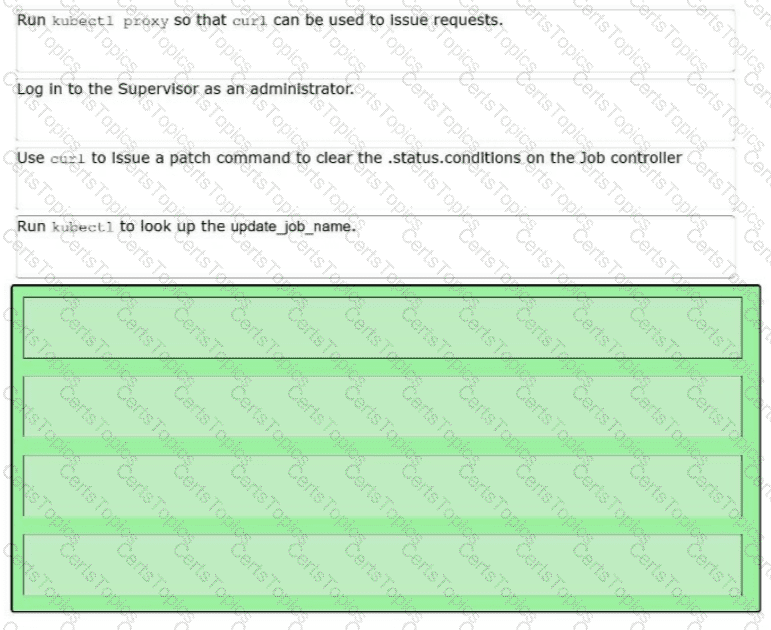
An administrator attempts to upgrade an existing Tanzu Kubernetes Cluster (TKC). The update fails and results in a cluster status of upgradefailed. Sequence the actions to troubleshoot the failure.
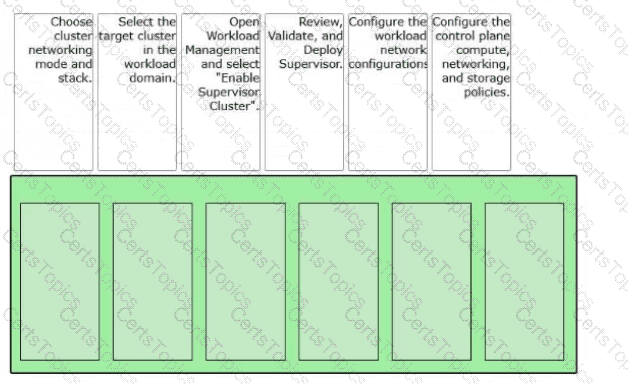
An administrator is tasked with enabling a Supervisor cluster in VMware Cloud Foundation (VCF).
Arrange the steps below In the correct order to complete the process of enabling a Supervisor In the environment.
What StorageClass is supported for VMware vSphere Kubernetes Service (VKS)?
A company standardized on the following configurations:
• vSphere Kubernetes Service (VKS) upgrade is separate from vCenter upgrades.
• A private registry will be utilized.
How should an administrator adhere to these standards?
How should an administrator enable autoscaling for a vSphere Kubernetes Service (VKS) cluster?
An organization has standardized on the following configurations:
vSphere Kubernetes Services upgrade is separate from vCenter upgrades.
A private registry will be utilized.
What is the recommended solution to adhere to these standards?
What Kubernetes object is used to grant permissions to acluster-wideresource?
An administrator is building a secure, multi-tenant container registry strategy for their vSphere Kubernetes Services deployment running on VMware Cloud Foundation. Each workload domain hosts a Supervisor Cluster, and multiple development teams require private repositories to store and distribute container images for Kubernetes clusters. The organization enforces strict image security posture due to compliance requirements. The operations team deploys Harbor as an add-on service through the Supervisor control plane, and developers push/pull images from Harbor through Kubernetes manifests.
What requirement describes the role and purpose of Harbor?
The DevOps engineer deployed a new application to a vSphere Kubernetes Service (VKS) cluster in a vSphere Namespace and then determined that a newer Kubernetes version was required. The vSphere administrator verified compatibility between the Supervisor and all running VKS clusters and successfully updated the vSphere Supervisor to the latest version. After the Supervisor update, the DevOps engineer still could not get the application to work.
What caused the application to fail?
What is the function ofContourin a VMware vSphere Kubernetes Service (VKS) cluster?
An administrator is updating a VMware vSphere Kubernetes Service (VKS) cluster by editing the cluster manifest. When saving, there is no indication that the edit was successful.
Based on the scenario, what action should the administrator take to edit and apply changes to the manifest?
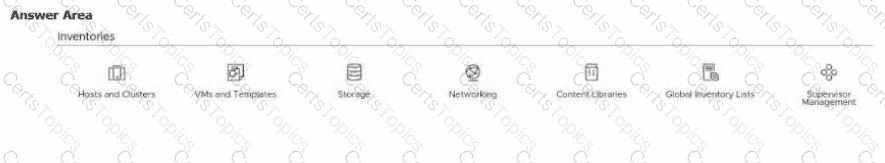
An administrator is configuring the Supervisor Service in vCenter.
Click the option an administrator uses to begin creating a vSphere Supervisor Zone.
An administrator is upgrading to VKS 3.4 and encounters the following error during cluster creation using workload, yami:
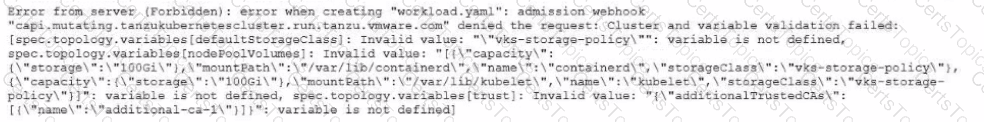
How should the administrator resolve this issue to successfully complete the upgrade " ?
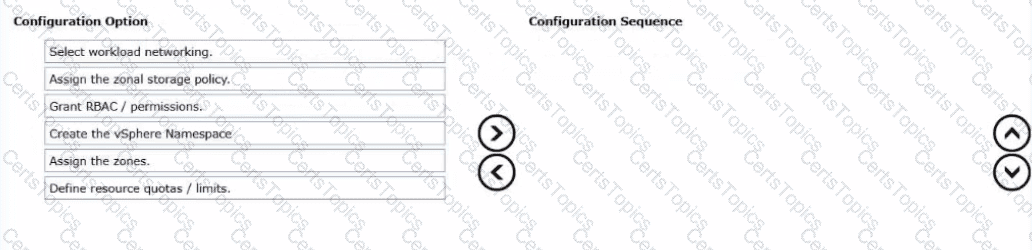
An administrator had deployed a Supervisor cluster on vSphere in a multi-zone-enabled environment and now wants to create a zonal vSphere Namespace so that workloads can be scheduled across zones.
Drag and drop the six actions into the correct order from Configuration Option list on the left and place them Into the Configuration Sequence on the right.
(Choose six.)
An administrator is tasked with installing Istio Service Mesh for VMware vSphere Kubernetes Service (VKS). Which command installs Istio?
Which type of storage is used by VMware vSphere Kubernetes Service (VKS) pods to store non-persistent data?
An administrator is deploying vSphere Kubernetes Service (VKS) to support containerized workloads across multiple regions. Each region hosts a dedicated Workload Domain with Supervisor instances deployed on vSphere Distributed Switch (VDS) networking. The organization’s security policy requires that pod-to-pod and pod-to-service communications be fully observable and controllable at the Kubernetes layer, without introducing additional licensing or overlay complexity.
When deploying a Supervisor, which CNI should the administrator select as the default supported option?
An administrator is upgrading an existing VMware vSphere Kubernetes Service (VKS) cluster and receives the following errors:
kubectl get nodes fails with memcache.go and “server is currently unable to handle the request”
couldn ' t get resource list for stats.antrea.tanzu.vmware.com/v1alpha1
yaml: mapping values are not allowed in this context
The administrator successfully updated the Supervisor, but an attempt to update the VKS cluster failed. Based on the scenario, what is the cause of the problem?
A cloud operations team is managing multiple Supervisor Clusters across two regions. Each region hosts its own vSphere Kubernetes clusters, integrated through a federated service mesh to enable consistent service connectivity and policy enforcement across environments.
The application team wants to expose a multi-tier microservice named “GovApp”, which includes front-end, API, and database services distributed between the two regions. Uniform traffic routing, identity, and security policies are also needed for these workloads regardless of the cluster or region in which they are deployed.
To meet these requirements, the architects decide to create a Global Namespace that spans both Supervisor Clusters.
Which two statements describe the requirements for a Global Namespace in a vSphere Kubernetes Service Mesh deployment? (Choose two.)
An administrator is deploying vSphere Kubernetes Service (VKS) on a VMware Cloud Foundation workload domain to support a new internal AI and data analytics platform. The environment must host both virtual machine (VM) applications and containerized workloads while maintaining a unified networking and security model through NSX. The design documentation outlines the requirements for the Supervisor infrastructure components.
What three components form the foundation of a VMware vSphere Kubernetes Service (VKS) Supervisor deployment? (Choose three.)
After upgrading the vSphere Supervisor, an administrator notices that the vSphere Kubernetes Service, configured as a Core Supervisor Service, is stuck in a“Configuring”state.
What should the administrator do to finish the upgrade?