What is an example of encryption at rest?
What is a use case for implementing information barrier policies in Microsoft 365?
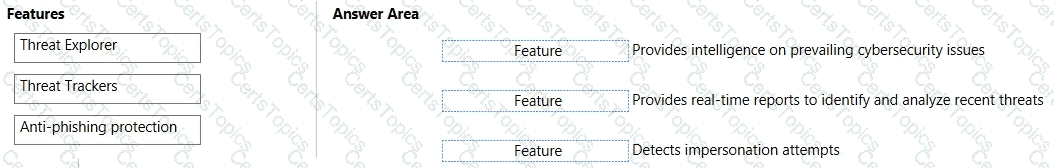
Match the Microsoft Defender for Office 365 feature to the correct description.
To answer, drag the appropriate feature from the column on the left to its description on the right. Each feature may be used once, more than once, or not at all.
NOTE: Each correct match is worth one point.
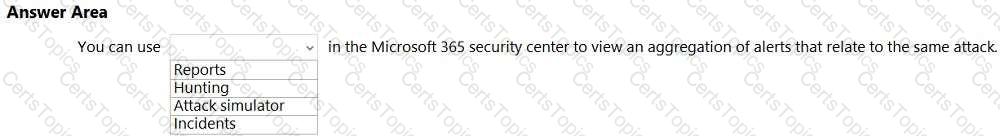
Select the answer that correctly completes the sentence.