Refer to the exhibit.]
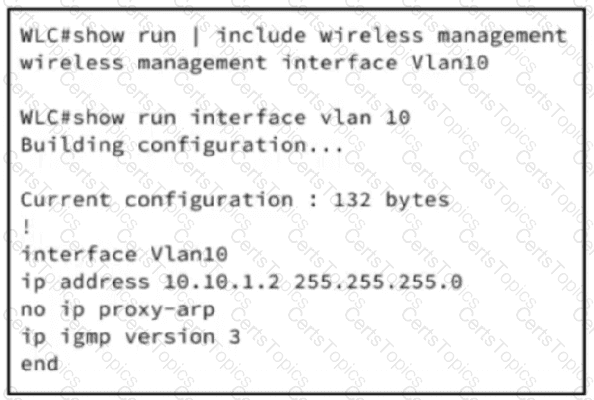
An engineer is setting up a new WLC in a branch office. The IT security policy states that all management access must use encrypted protocols, administrators will connect remotely, and network scans will be run to check for any noncompliant management protocol exposure. Which action must the engineer take to achieve the required management access policy?
What is a benefit of applying TACACS authentication for device access?