In which part of the SMTP conversation can threat actors spoof information to make the message look safe to the recipient?
What is a defining characteristic of Advanced Persistent Threat (APT) actors?
Which two tasks are considered frequent and high-priority when actively reviewing the threat landscape? (Select two.)
An attacker registers a domain like “great-company.com” to impersonate “greatcompany.com.” What tactic is being used?
Under what circumstances will TAP generate an email notification alert?
An analyst has been tasked with providing a report that can be used to prioritise investigations based on a user's Attack Index score. Which report would be most suitable for this purpose?
An analyst is reviewing a quarantined threat within Threat Protection Workbench.

Based on the indicators shown in the exhibit, what is the most likely reason the threat was quarantined?
An analyst wants to use the Threats page in TAP Dashboard to review all messages related to a phishing campaign that contain an attachment. What is the correct method to filter these messages?
Which of the following is a useful training exercise for security analysts?
When filtering for threats on the TAP People page, which two filters have the highest chance of finding compromises? (Select two.)
An analyst is reviewing the Threat Response Quarantines card for a message in TAP Dashboard, as shown in the exhibit.
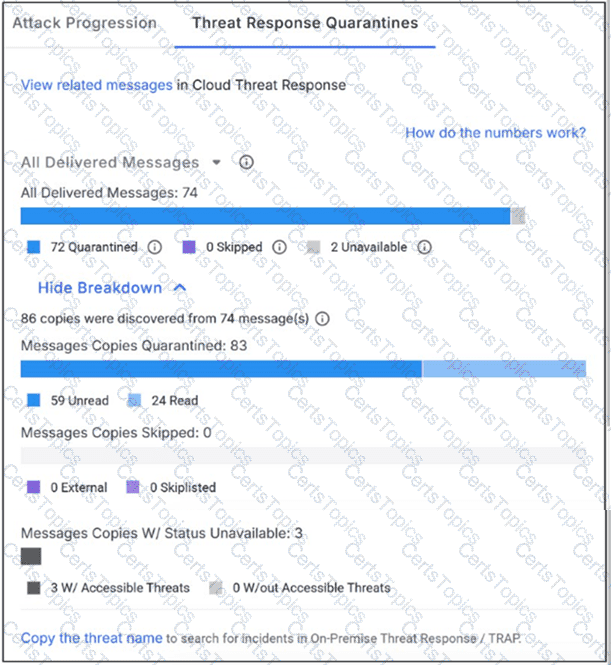
Why might a message be flagged with status “unavailable”?
Refer to Exhibit:
X-Proofpoint-Banner-Trigger: inbound
MIM-version: 1.0
Content-Type: multipart/mixed; boundary="boundary-1698346305"
X-CLX-Shades: MLX
X-Proofpoint-Virus-Version: vendor=baseguard
engine=ICAP:2.0.272,Aquarius:18.0.987,Hydra:6.0.619,FMLib:17.11.176.26 definitions=2023-10-26_22,2023-10-26_01,2023-05-22_02
X-Proofpoint-Spam-Details: rule=spam policy=default score=89 bulkscore=0 phishscore=0 mlxlogscore=-91 suspectscore=0 malwarescore=0 adultscore=0 spamscore=89 classifier=spam adjust=0 reason=mlx scancount=l engine=8.12.0-2310240000 definitions=main-2310260209
In the process of reviewing a false positive, you see the following email header. What was the reason the message was quarantined by the Proofpoint Protection Server?
What is the purpose of Smart Search?
As a security analyst, you need to update the TAP URL Defense Custom Blocklist. Which three entries are valid formats for the blocklist? (Select three.)
You would like to view the total number of uncleared threats or false positives that have been interacted with by users over the past 2 weeks. How can this be accomplished on the TAP Dashboard?