While configuring a new security policy in a Nutanix microsegmentation environment, an administrator wants the policy to remain flexible even if virtual machines change subnets or obtain new IP addresses. Which configuration approach should the administrator use when defining the policy scope?
An administrator needs to use Prism Central to identify a subnet belonging to a VPC. How can the administrator identify networks associated with a VPC within Prism Central?
An administrator has observed the following message: Which two statements most accurately describe the security hitlog captured above? (Choose two.)
Exhibit:
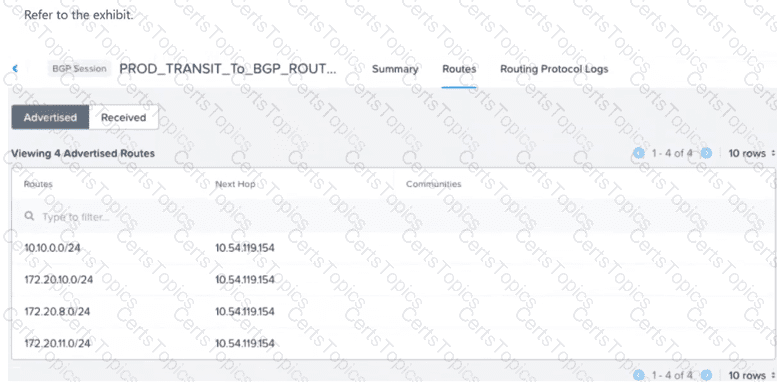
A VM with IP address 172.20.9.5 resides on a subnet with CIDR 172.20.9.0/24. The VPC is successfully peered via BGP with an external router... External networks outside the VPC are unable to reach the VM. What configuration change should be made to enable reachability for the VM?
When creating a VPC, enabling the Transit VPC toggle changes the role of the VPC. What does the Transit VPC toggle do?
Refer to Exhibit:
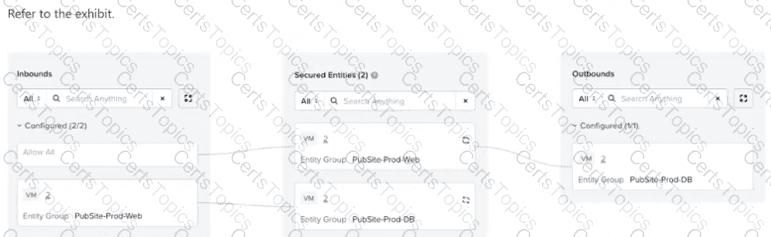
An administrator is tasked with configuring an application policy for a two-tier public website with Web and DB components. The database servers need to communicate with each other for replication, but the web servers should not be able to communicate with each other. The administrator configures the policy... and sets it to Enforce mode. Later testing reveals that the web servers are able to communicate with each other. What should the administrator do to resolve this?
An administrator notices that several VMs in a Nutanix AHV cluster are intermittently losing network connectivity. In Prism Central, a critical alert appears: "Network Function VM (NFVM) packet processing delays" What is the next step that the administrator should take for this issue?
An administrator is designing a new Transit VPC to service multiple Tenant VPCs. While adding subnets, the administrator must choose the correct network type supported by Flow Virtual Networking for this VPC. Which network type is supported for subnets inside a Transit VPC in Flow Virtual Networking?
An administrator recently deployed a new set of virtual machines... 3-tier web application... restricted as follows: Only application VMs can talk to database VMs on port 3306 Frontend VMs should only communicate with application VMs on port 8080 Which action will correctly create and configure the Security Policies in Nutanix Flow to satisfy this task?
Flow Network Security Next-Gen is supported in which two environments? (Choose two.)
Which step is required before placing the Flow Network Security software bundle on a local web server?
An administrator is building a VPC... VPC CIDR: 10.10.0.0/16 Subnet CIDR: 10.10.10.0/24 "Ext_Net_Ext" (NAT): 192.168.1.0/24 "Ext_Net_Internal" (Routed): 172.16.1.0/24 The on-premises application server has an IP address of 172.16.2.50/24. A VM (10.10.10.100) in the VPC Subnet can reach the internet but cannot reach the on-premises server. Which static route needs to be added to the VPC route table to resolve this?
An administrator has created a VPC with the following subnets: 10.1.1.0/24 10.1.2.0/24 10.1.3.0/24 What action must be taken for these networks to be externally routable?
Users have recently reported intermittent connectivity issues and slower-than-usual application performance for a Nutanix cluster to an administrator. The administrator needs to identify the root cause of these issues by analyzing the health of the infrastructure components. What action should the administrator take first to diagnose the root cause of the problem?
An administrator receives a ticket reporting unwanted traffic between production and development servers. The administrator reviews the Flow Network Security logs and finds the following:
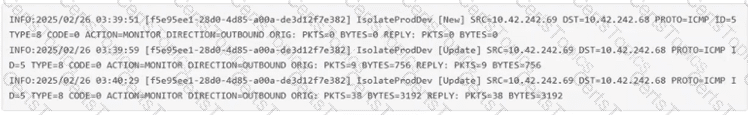
How can the administrator resolve the issue?
An administrator manages a four-node cluster Each node has a 4 available 10GB uplinks, and all four are configured as an Active/Active bundle. They want to use Flow Virtual Networking to provide networking to the VMs in the cluster with the following requirements: VMs should be in a single VPC. VMs should be reachable by their real IP addresses. The VPC should have access to the most north/south bandwidth possible. No changes can be made to the physical infrastructure. How can this best be achieved?
An administrator wants to configure the subnet 10.1.1.0/24 to stretch across two VPCs over a Network Gateway in VXLAN mode. The VMs on this subnet need to communicate with a traffic pattern of size 2000 Bytes. What is the minimum MTU required in the underlay network to ensure communication happens without fragmentation or traffic drops?
An administrator needs to isolate communication between VMs in Production and Development environments. Each VM is categorized by Environment and Site category values. The administrator wants this isolation to apply only to VMs located at Site: Branch-001. Which configuration best meets the requirement?
An administrator is building a new VPC in Prism Central to isolate a test environment. The administrator plans to connect it to an external network later, but they want to complete the initial creation first. Which configuration items are the minimum required to successfully create the VPC?
What does placing a policy in Monitor mode accomplish?
A customer wants to migrate VMs from a VLAN Basic Subnet to an Overlay Subnet with the same IP prefix. Which migration approach ensures minimal disruption?
An administrator sets up a VPN between two Nutanix VPCs in different Availability Zones. After deployment, the VPN tunnel shows as Up, but traffic between the VPCs is not flowing. Which configuration step is most likely missing?
A customer wants to extend a VLAN subnet to a remote data center using VTEP. The administrator configures a Subnet Extension which shows UP in the Prism Interface, yet traffic fails to pass. Which setting is most likely misconfigured?
An organization plans to apply security controls based on user group membership in Active Directory. What configuration is required in Prism Central before VDI policies can be used?
During a security review, the administrator confirms that the existing security policy does not explicitly allow traffic from Environment: Development to Environment: Production. A VM in the Development category was still able to reach a Production VM over IPv6. What is the most likely cause of this behavior?
A new multi-tier application is being deployed across several subnets in a Nutanix environment. The security team wants to create a Flow Network Security Policy to restrict traffic between the tiers, but the complete matrix of required network ports and protocols is not fully documented. Which strategy should the team employ first to accurately capture the necessary communication patterns without risking application outage?
The alert details mention a specific external network. Attempts to assign new Floating IPs to VMs fail, but existing Floating IPs continue to work. What is the cause of this alert?
An administrator has a VPC with multiple overlay subnets and a VPN gateway configured for site-to-site connectivity. During testing, the administrator noticed fragmented packets and poor performance. Which configuration change resolves this issue without disabling VPN?
When configuring an Application policy, an administrator defines a VM Category Application:MySQL as a Secured Entity. The administrator wants to ensure that traffic between VMs in the Secured Entity is kept to only required replication traffic on the default mysql service port. How should the administrator best accomplish this?
Which action allows an administrator to reuse a single existing policy in a different scope?
An administrator is designing a VPC for a three-tier application. The workloads must communicate with the Internet using source NAT and also communicate with on-premises networks 10.50.0.0/16 and 172.20.32.0/20 with no address translation. In the Create VPC dialog, the administrator can associate external subnets and specify destination prefixes. Which configuration satisfies the requirements?