Refer to the exhibits.
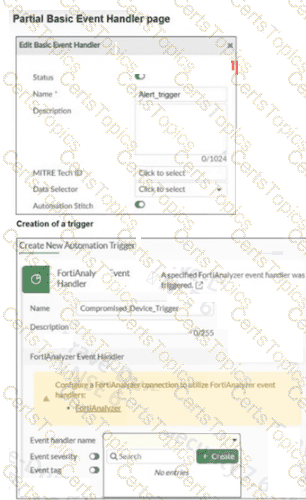
A partial Basic Event Handler page on FortiAnalyzer and the creation of a trigger in a FortiGate device are shown. To improve the protection of your OT network, you want to automate the handling of compromised devices notified through FortiAnalyzer. You have configured an event handler named Alert_trigger as shown in the exhibit. When you create the trigger on the FortiGate device, the Event handler name field does not provide the Alert_trigger option. What two actions must you perform to make the Alert_trigger option available? (Choose two answers)
During layer 2 polling , which two pieces of information are gathered by FortiNAC to identify a device? (Choose two answers)
You want FortiAnalyzer to trigger an automation stitch on a FortiGate device automatically. What must you configure on FortiAnalyzer to enable direct communication with FortiGate? (Choose one answer)
In the Purdue model, at which level are physical assets like the Industrial Internet of Things (IIoT) placed? (Choose one answer)
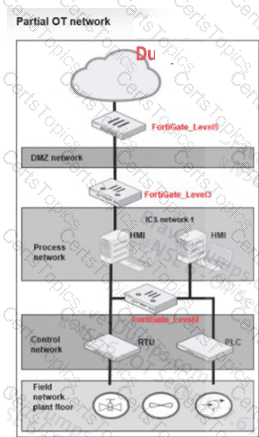
Refer to the exhibit.
A partial OT network is shown. You have encountered many disconnections in the links and want to improve the availability of this network. Which action can you perform? (Choose one answer)
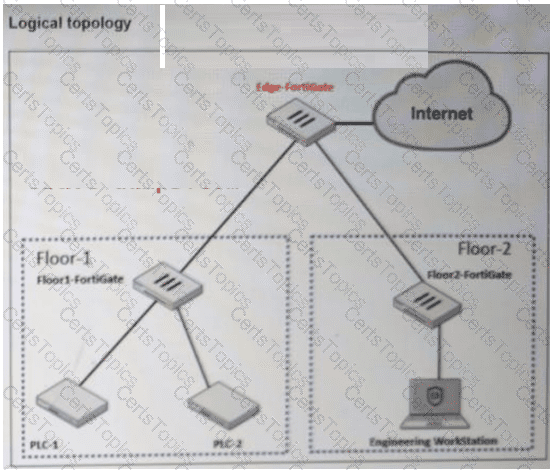
Refer to the exhibit.
A partial OT network is shown. In this OT network, you must add additional security measures to detect OT protocols and, therefore, increase the traffic visibility. Which security sensor must you implement to detect the OT protocols in this network? (Choose one answer)
You want to improve access control for your large OT network using passive authentication. What must you configure on FortiGate? (Choose one answer)
According to the IEC 62443 standard, your security level is 4 . What is your OT environment defending against? (Choose one answer)
Refer to the exhibit.
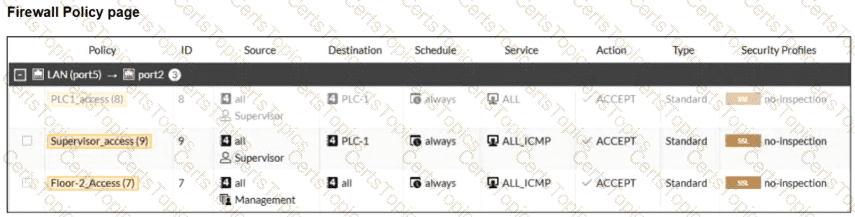
A firewall policy page is shown. To improve the security of your OT network, you have configured a Supervisor profile in the firewall policies, as shown in the exhibit. However, a supervisor is reporting that he cannot ping PLC-1. What are the two reasons? (Choose two answers)
You want to improve the security of your OT network and therefore deploy a FortiGate device with the OT signatures database. Which two statements about this database are true? (Choose two answers)
Refer to the exhibit.
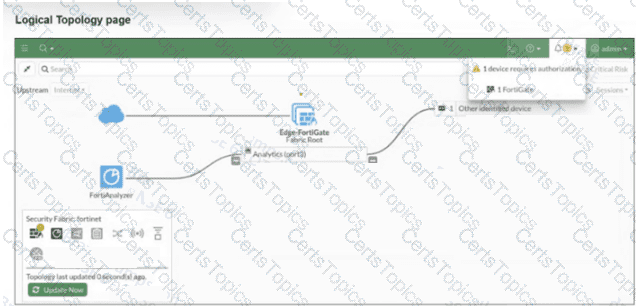
A Logical Topology page of a FortiGate device is shown. Your OT company wants to gain visibility into the network. You decide to implement device detection with the Security Fabric. Based on the exhibit, which statement is correct? (Choose one answer)
What is the next step if FortiGate cannot detect a device locally? (Choose one answer)
You want to protect OT devices that are not updated against known vulnerabilities so you apply virtual patching to the firewall policies. What must you check to confirm that the OT devices are virtually patched? (Choose one answer)