You determine that there are a large number of samples on FortiSandbox that are obsolete and no longer needed for future analysis. Which CLI tool must you use to remediate this issue? (Choose one answer)
You notice a recent file downloaded by some end stations is exhibiting malware behavior, however, on the sandbox the file is rated clean. After further investigation you determine that only end stations using the Opera browser are being affected. What must you do to prevent these infections? (Choose one answer)
A FortiSandbox HA cluster is configured with the MTA adapter. What does the primary node do when it receives MTA jobs? (Choose one answer)
How can you limit an administrator ' s access to scan jobs on FortiSandbox based on the system that submitted the scan request? (Choose one answer)
You must increase the scanning capacity of a FortiSandbox device by increasing the number of clones, but the FortiSandbox local clone limit is already at maximum. Which two actions can you take to expand the scanning capacity of the unit? (Choose two answers)
An organization has an existing FortiGate provisioned as a data center firewall (DCFW) that submits inbound files to FortiSandbox for inline scanning. As a result of a network redesign, traffic between the FortiSandbox and the DCFW now passes through an intermediate firewall. Inline scanning is no longer working. While examining the configuration of the intermediate firewall you notice that it is configured to allow traffic on ports TCP/3389, UDP/53, and TCP/443. What must you change for the integration to work? (Choose one answer)
Refer to the exhibits.
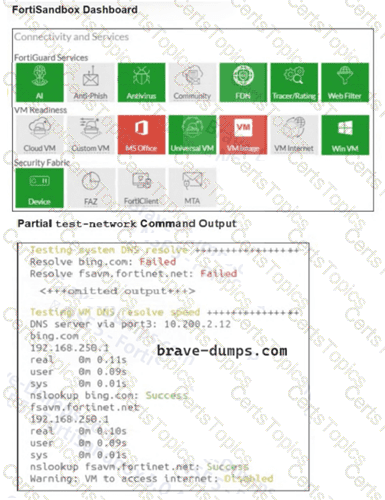
You are unable to download guest VMs on a new FortiSandbox VM. What is the reason for this? (Choose one answer)
A FortiSandbox VM has been deployed and has been functioning correctly for several months. Suddenly, the system begins rejecting file submissions with an error message indicating a licensing problem. How can you determine, using the CLI, if the license is still valid? (Choose one answer)
Refer to the exhibit.
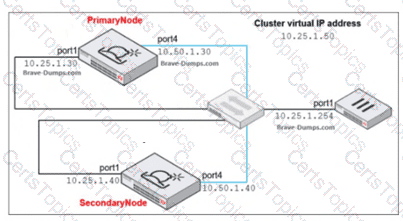
Which command must you use to configure the FortiSandbox device as the primary node? (Choose one answer)
Which stage of the Cyber Kill Chain does FortiSandbox and FortiClient EMS integration help to block? (Choose one answer)
You are asked to create some custom VMs to better represent your security environment. In which two FortiSandbox deployments is this supported? (Choose two answers)
Which two products integrated with FortiSandbox work to protect against the lateral movement stage of the Cyber Kill Chain? (Choose two answers)