Which function is most appropriate for extracting fields from logs formatted as key=value pairs?
Which command helps visualize in real time whether sources and sinks are working properly in the Log Collector?
How can you enable internal logging for a specific Falcon Log Collector instance from the Fleet view?
As a Next-Gen SIEM Engineer, you are responsible for managing and tuning correlation rules to improve the detection of potential security incidents. One of your correlation rules is designed to detect multiple failed login attempts that are followed by a successful login within a short time frame.
Which step would you take to tune this correlation rule to reduce false positives while maintaining its effectiveness?
What is the primary benefit of utilizing Next-Gen SIEM’s built-in dashboards?
A correlation rule is generating a high volume of detections. You have been asked to temporarily deactivate it so your team can investigate.
What will happen to previously generated detections while the rule is in a deactivated state?
Review the log sample below:
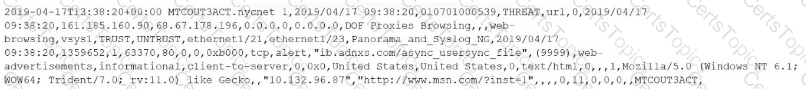
What type of parser should be used to extract fields and values from this log?
What should you do with a field that is not CPS-compliant when adding it to a parser?
What are the four required CPS-compliant Event parser tags?
Which Falcon LogScale Collector output format would you use if your downstream SIEM requires raw nested event data?
You notice that the format of incoming logs suddenly changes from JSON format to key-value pairs during log collection.
What action would you take to parse the data correctly?
Which three System alerts are enabled by default in Next-Gen SIEM for third-party connectors?
You are reviewing a lookup file to determine whether an event was successfully parsed during ingestion.
Which metadata field indicates the event’s parsing status?
You are performing a search query using data from the Falcon Sensor and third-party data connectors.
Which Advanced Event Search data source should you choose?
Which field is compliant with CrowdStrike Parsing Standard (CPS)?
You find a Falcon Log Collector instance on a Linux system that is not connected to Fleet Management.
What command would you use to enroll the Falcon Log Collector?
Which Falcon LogScale Collector mode keeps the log source configuration stored locally on the collector host instead of centrally in Fleet Management?